Cybercrime , Cybercrime as-a-service , Fraud Management & Cybercrime
Update: Samsung Confirms Source Code Stolen in Breach
Lapsus$ Posts Samsung Data Just a Day After Leaking Nvidia Credentials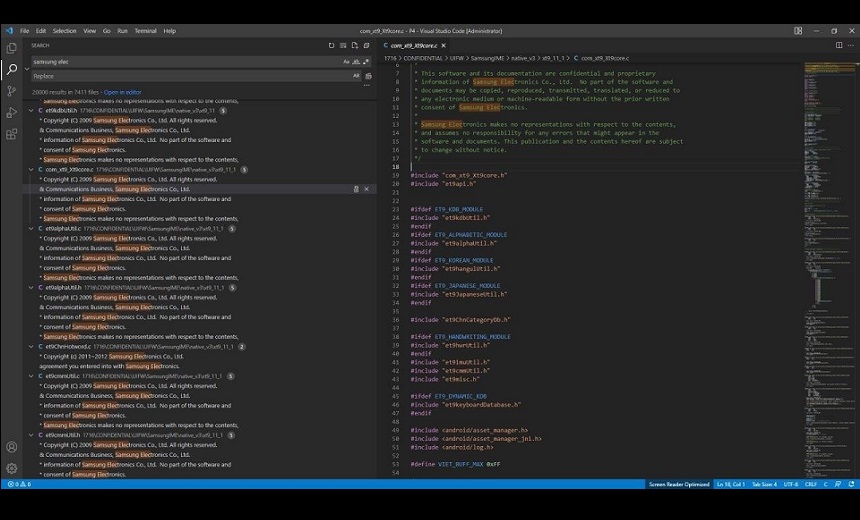
South Korean consumer electronics giant Samsung Electronics has confirmed to Information Security Media Group that it has suffered a breach that includes source code being stolen. Ransomware gang Lapsus$ has leaked a massive collection of confidential data from Samsung just a day after leaking credentials of 71,000 Nvidia employees.
See Also: Ransomware Response Essential: Fixing Initial Access Vector
ISMG verified that the alleged leak had been posted by the Lapsus$ gang on its official Telegram channel, which had 13,724 subscribers as of Saturday.
On Monday, Samsung responded to ISMG requests for further information with an official statement, saying: "We were recently made aware that there was a security breach relating to certain internal company data. Immediately after discovering the incident, we strengthened our security system. According to our initial analysis, the breach involves some source codes relating to the operation of Galaxy devices but does not include the personal information of our consumers or employees. Currently, we do not anticipate any impact to our business or customers. We have implemented measures to prevent further such incidents and will continue to serve our customers without disruption."
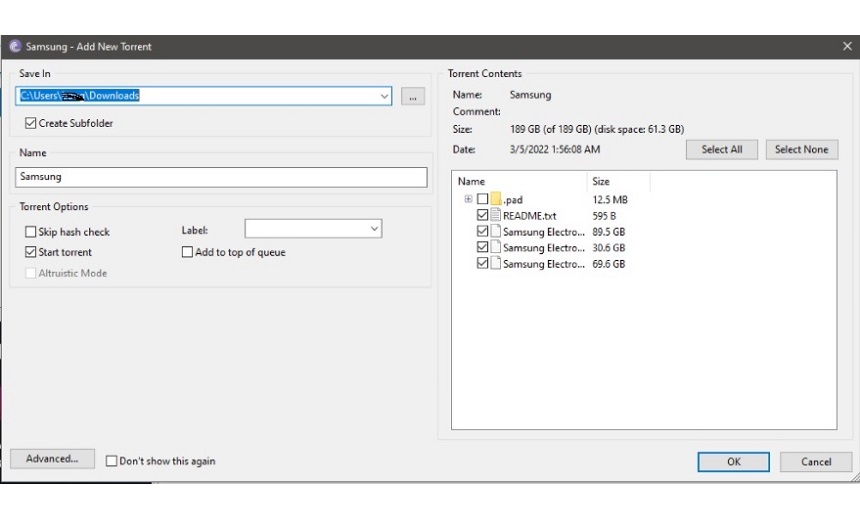
The gang has posted a torrent file of 190GB of Samsung data.
LAPSUS$ extortion group have successfully breached both NVIDIA & Samsung.
— vx-underground (@vxunderground) March 4, 2022
-March 1st: They demand NVIDIA open-source its drivers, or else they will
-March 4th: LAPSUS$ released Samsung proprietary source code.
See attached images for more details directly from LAPSUS$ pic.twitter.com/U3VD7R2KRl
Leaked Material
The ransomware group released a teaser on its Telegram channel before posting the data saying, "get ready, Samsung data coming today." Then the gang posted confidential Samsung source code data in a compressed file, available on torrent, and split it into three parts, which include almost 190GB of data.
Lapsus$ published a description of the leak, which it says includes source code for every Trusted Applet installed on all Samsung device's TrustZone with specific code for every type of TEE OS (QSEE, TEEGris, etc). Trusted Applets are used for sensitive operations such as full access control and encryption. The group says it also includes DRM modules and Keymaster/Gatekeeper.
Algorithms for all biometric unlock operations include: "Source code that communicates directly with sensor (down to the lowest level), we're talking individual RX/TX bit streams here and boot loader source code for all recent Samsung devices, including Knox data and code for authentication," the gang says.
The gang also says it has various other data, including confidential source code from Qualcomm. It is yet not clear if Lapsus$ has tried to ransom Samsung, as it did in its previous campaign with Nvidia.
The group also says that it offers Samsung activation servers source code for first-time setup and Samsung accounts full source code that includes authentication, identity, API, services, and many more.
Pascal Geenens, director of threat intelligence at Radware, says ransom notes sent by email or posted on Twitter do not always find their way to right people in the organization. "We have seen ransom notes sent to the wrong branch on the opposite side of the globe, instead of the branch the actual attacks were hitting."
"We regularly see notes delivered through payload or meta data, for example the 'user-agent' header, in web requests that are scanning for vulnerabilities. Sometimes those notes are referring to white hats or internet scanners or sometimes threat hunters are using them to leave behind their contact details, and at other times it is attackers rick-rolling or leaving obscene messages," Geenens says.
Geenens agrees that delivering a note inside the attack is a new technique we have not seen before. "From the attacker point of view, this technique might help them to automate attacks," he says.
"They do not need to put in effort to find the right email addresses and contacts for delivering their note. This technique could also lead the way to scale ransom DDoS to a new level by ‘spraying and praying.’ Compare it to hoax RDoS campaigns we have seen in the past, sending out ransom notes but never following up with an actual attack. Hoax campaigns scale well but lose traction very fast as they get detected and reported without actual follow through attacks," Geenens says.
Lapsus$ Growing Attack Surface
Lapsus$ group first came to public attention in December 2021 following a ransomware attack on websites owned by Brazil's Ministry of Health. The group claimed to have stolen and subsequently deleted around 50TB of data from the ministry’s systems.
Earlier, chipmaker Nvidia was reported to have suffered a massive outage after a security incident claimed by Lapsus$ affected the company's developer tools and email systems (see: Chipmaker Nvidia Investigating Potential Cyberattack).
The threat actor shared a download link on its Telegram channel to an 18GB data dump that it says contains 1TB of stolen confidential data.
Nvidia published a report acknowledging that a threat actor had stolen employee passwords and undisclosed Nvidia proprietary information from its systems. This data, it added, has been leaked online.
"On February 23, 2022, Nvidia became aware of a cybersecurity incident, which impacted IT resources. Shortly after discovering the incident, we further hardened our network, engaged cybersecurity incident response experts, and notified law enforcement," the company says in its report.
The Lapsus$ ransomware group later released a portion of the highly confidential stolen data, comprising source codes, GPU drivers and documentation on Nvidia's fast logic controller product, also known as Falcon and Lite Hash Rate or LHR GPU (see: How Lapsus$ Data Leak May Affect Nvidia and Its Customers).
On Wednesday, the hacking group demanded $1 million and a percentage of an unspecified fee from Nvidia for the Lite Hash Rate bypass. Nvidia's LHR reduces Ethereum cryptomining capabilities by 50% without compromising gaming performance but this bypass fully restores Ethereum mining performance.